So here I am signing on for the Australian Government's online Medicare thingy, which started out pretty secure. You do the first stage of the signup stuff, and then they send you a letter with your password for the next stage of the signup in it.
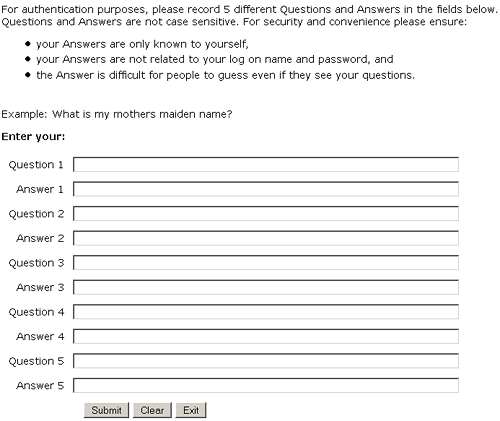
And then, after you log in using that password, you get this:
Make sure your Answers are only known to yourself! You know, like your mother's super secret maiden name that not even SHE knows!
(And yes, the missing apostrophe's the icing on the cake.)
I know this kind of crap is nothing new, but this is a pretty awesome implementation of it.
Not only do they tell you to use the archetypal, perfect example of an appallingly insecure "secret question", but they also tell you to set up four more such questions. So even if your first question is quite a good one, like "What poster did I have on my bedroom door before I had the Van Halen one?", you're likely to come up with something a lot less secure as you add more and more of the bloody things and run out of ideas.
(Here's another one that forces you to have five questions. Bonus points for the versions that won't let you enter an answer with fewer than six characters. Because nobody's called Smith or Jones.)
I came up with a properly obscure but memorable question for the first of the five on the Medicare form, then entered keyboard-mashing randomness for the other four. Then I wondered whether these "authentication" questions might be asked at some time other than when I'd forgotten my password - if they're used all the time, possibly even over the phone, then making one of them "Dummy question 3? / sdtrt45ruidhbioweyrvga34awe7du" is probably not a good idea.
So I tried duplicating my good first question and answer for the other four as well, despite the fact that the instructions tell you to record five different ones. That turned out to be fine.
(I've now discovered that the Medicare site uses the "security questions" when you want to change stuff like your contact details. It asks you two of the questions then, so it's a good thing I didn't just bang my face on the keyboard. Because all five of my questions are the same, the system of course just asked me the same question twice. It didn't seem to mind.)
It's possible to wring some security out of even a system that forces you to use mother's-maiden-name as an authentication question, by simply making up a novel answer for that question. But if you use the same oddball "maiden name" for authentication for every such site, then the first time the information that your mother's maiden name is "snorkel" gets out - which you should assume it's going to, because these people have demonstrated themselves to be idiots by their choice of this security system in the first place - you're just about as screwed as you would be if you'd used the real, matter-of-public-record maiden name.
To get around this, you have to come up with a different "maiden name" for every site that asks. You of course won't be able to remember them all unaided, so will need to store them along with your other passwords. Since the only time you're likely to need the "maiden names" is when you've lost the other passwords, though, this brings one face to face once again with the blatant stupidity of the whole concept.
And yes, the blithe suggestion of "maiden name" secret questions also skates over the issue of people whose family doesn't have a vanilla Western surname at all. Not to mention foundlings, people who had the hide to be born to unmarried parents, and that so-often-neglected portion of the information security marketplace, humaniform robots.
("My mother? Let me tell you about my mother.")
UPDATE: How did that guy "hack" Sarah Palin's Yahoo e-mail account?
That's right: By taking advantage of "secret questions" that were matters of public record, or otherwise trivially easy for anyone to guess.
(It's a shame that Palin didn't use that account to do anything very interesting. Wouldn't it have been awesome if it turned out that was the account she used to indulge her secret passion for Mythbusters slash stories?)
1 February 2008 at 1:04 pm
The Medicare Online Services Frequently Asked Questions page helpfully provides ten examples of secret questions.
Seven of them are matters of public record.
If an attacker has a friend at the car registration department, two of the remaining questions are also answerable.
And if "your first pet" was one that required registration, someone could well figure out the answer to the last remaining question, too.
Every example they provide is actually an example of exactly the kind of thing you should not use as a "secret question".
I am enormously pleased that my private medical information is in the hands of people who do not seem to have any comprehension of what "a secret" actually is.
1 February 2008 at 3:04 pm
I have a terrible time with passwords, with my many PWDs becoming more complex over time. It is not fun to forget a password to something important; you either hit a phone-droid who won't let you guess again, or you get (even scarier) the type who give you clues FFS! You then realise your password is stored plain text, which pretty much defeats the whole system. I know for certain
St.Georgea Local Bank does this, as some nit there typed my original password incorrectly, so I alsways get it wrong, and they give me hints till I get it. I've had "close enough" as a response sometimes, which seems to indicate the staff view it as just as much of an inconvenience as I do.And...
You learn something new every day.
So is the COP .357 a real gun? It would likely have a bit of a kick if you fired all 4 barrels. IRCC the film script said his gun was a 'black hole gun' or 'quantum singularity gun' or some such. If you frame-by-framed the DVD you can see that they tried to show this as a black 'laser bolt' type effect. A neat concept, but totally lost as it appears on about 3 frames of film. Neat trivia though. I don't regularly watch Bladerunner frame by frame though. Only once or twice.
1 February 2008 at 4:13 pm
Hurrah! rejoice in another victim of the bowel loosening, wrist grating, teeth shatteringly awful guvmunted "online service"
After filling out a twenty page form full of circular logic my login questions were changed along the lines of "How bad is this website?", "how much do you hate this website?" "how would you like to kill those responsible for creating it?" All with VERY memorable answers.
1 February 2008 at 5:48 pm
In Puerto Rico, everyone knows your mother's maiden name http://healthhacker.org/satoroams/?p=788 causing fraud problems for Citibank because their secret question was that. Their solution? Nope, not changing the question, but preventing transfer between Citibank PR and Citibank US. A comment notes you can put anything as the answer to the question, so you could pretend to be descended from the Froblewitzes.
1 February 2008 at 5:56 pm
Plus -- the incorrect capitalisation.
1 February 2008 at 7:14 pm
Gotta love the suggestion "How many brothers and sisters do I have?" for a secret question. Do you think it might be possible to have a lucky guess at the answer?
1 February 2008 at 7:56 pm
It's not entirely related to dodgy online security, but I applied for an Australian passport last year using the online system. It's basically a series of standard webforms which generates a pre-filled PDF application form which you've then got to print, sign, take to post office etc.
One of the pages in the web-based section (which looks nothing like the final PDF) asks you to enter your email address in a textbox, with the note "Please print clearly in block capitals only" alongside. Well, I typed as clearly as I could...
Once I logged in a few days later to check the progress of my application, I noticed my email address had been OCR'd as m1ke@nw.com.aw - so apparently my typing wasn't as clear as I'd thought.
1 February 2008 at 10:57 pm
I love this all this 'secure' "multi factor" web authentication is still based on the what you know security system. Of course all it takes is one key logger or one man in the middle attack and it doesn't matter how good your secret questions are the attacker has the answer.
The commonwealth bank has slightly better two factor auth. They make my log in with a userid and password to do all my online banking. Then they have my mobile number on file and SMS me a one time use token each time I want to change details or add a new transfer destination. This verifies that I have my phone. So I know something AND I have something, that's two factor auth.
There is still the possibility of MITM attacks but it requires more work for the attacker.
thedailywtf.com had a whinge on this a while back:
http://thedailywtf.com/Articles/WishItWas-TwoFactor-.aspx
1 February 2008 at 11:17 pm
If you think it's bad having to answer five such questions, you'd be horrified at a bank I dealt with. I'd been a customer for about ten years when, a year ago, they added this bullshit "security" feature to their online banking site, requiring me to pick (and answer) *sixteen* such questions from their predefined set of of questions -- virtually *all* of which were matters of public record, and could be answered about anybody reasonably-well connected using Google.
They would require you to answer one of these questions at random times, or anytime you wanted to do something "novel", like add a new bill to your list of bills that you could pay online.
I argued with their phone-support people, and on up the chain to an assistant-to-the-assistant-security-manager, none of whom seemed to have the first understanding of computer security.
I switched banks -- chequing, savings, investments, everything -- and left them. The manager of my local branch was very understanding, but powerless to do anything about the policy.
2 February 2008 at 6:34 am
Just be thankful you don't have your personal information in the UK... Big Brother over here has decided it is a good idea to have a single Identity Card (Australia Card... Anyone?) which will be used to store all of the personal information relating to honest law abiding citizens. There is absolutely no reason why this is not a good idea...
Feb 2007 - Government admits 80 passports are lost in the post every month (I have recently been asked to post my actual passport to the Driver's Licencing Authority, I am so looking forward to that).
Nov 2007 - Her Majesty's Revenue and Customs (basicly the customs and tax offices combined) had lost CDs containing personal data, with all information on all British families with children under the age of 16 (around 25 million people). HMRC then sent out apology letters that also contained sensitive personal information. The boss of the HM Revenue and Customs has admitted there have been seven other significant data losses in recent years. Sophos conducted a poll of 350 in which 58% of the responses were; "Inevitable".
Dec 2007 - The Transport Secretary admitted that the details of three million learner drivers had gone missing when a hard drive was lost in Iowa (raising the question... what was UK drivers info doing in Iowa?).
Dec 2007 - CDs with personal information on thousands of benefit claimants were found at the home of a former contractor to the Department of Work and Pensions (that's right... A contractor!).
Dec 2007 - The names, dates of birth and national insurance numbers of 45,000 people claiming benefits in west Yorkshire were lost by the Government.
Dec 2007 - Department of Health has said that data losses were being dealt with individually by the relevant trusts (hospital management) and that it therefore did not have details of how many patients' records were lost, City and Hackney Primary Care Trust, in east London - has reportedly lost the details of 160,000 children
Jan 2008 - Secretary of state for defence Des Browne has admitted that the laptop lost by the Ministry of Defence containing details of up to 600,000 defence personnel was not encrypted, and also that services personnel have previously lost two more laptops containing similar unencrypted recruitment information.
I could go on but I think you get the idea. I am so longing to return home to Australia where the worst I have to worry about is a slack security system... Over here they seem to just give out unencrypted laptops/discs, brimming with citizen's personal information, to that bloke outside who wears his underpants on the outside and hope for the best.
4 February 2008 at 9:36 am
think about tiawan. they have a system already in place but it gets worse. if you don't have this card, you are not a citizen of the nation. eg no school for you and no medicare
5 February 2008 at 8:59 am
Short version of my own Medicare website war story: On the advice of Bruce Schneier, I typed gibberish into the secret questions. Then I found that to get "higher access level" I had to retype two of the five gibberish answers that I had provided earlier. Which meant that I had to dig them out of my firefox autocomplete memory.
A bigger fiasco I cannot imagine. No, actually I could, but I don't want to.
5 January 2015 at 10:38 pm
[…] In fact, they’ve been badly implemented since their inception, and were worse than useless even 7 years ago. […]